The Uffizi Cyberattack: a Warning for Heritage Institutions, but not a simple story
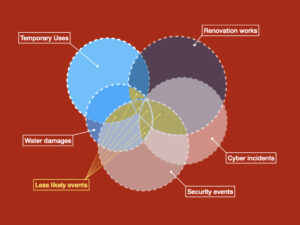
The Uffizi cyberattack is a warning that heritage security is now inseparable from cybersecurity. When access data, camera positions, and operational information are compromised, the impact can extend from digital systems to physical protection, evacuation control, and fire safety.

A Room of the Uffizi Gallery in Florence (Italy). Image: Marta De Bortoli1991, CC BY-SA 4.0 <https://creativecommons.org/licenses/by-sa/4.0>, via Wikimedia Commons
On 2026, the Uffizi Galleries in Florence, became the focus of a cyberattack story that quickly moved beyond technical disruption and into the wider debate on heritage security. What is confirmed is that malware hit the museum’s administrative systems in late January and early February, affecting staff email and internal computers, while visitor services, ticketing, surveillance, and public access remained operational.
The cyber incident affecting the Uffizi has quickly become more than a local security story.
It is now being read as a test case for how cultural institutions communicate risk, separate fact from speculation, and respond when digital disruption enters the world of heritage protection. What is confirmed is that the museum suffered a malware attack on its administrative systems in late January and early February 2026.
Staff email and internal computers were affected, and the incident prompted an investigation by Italian authorities. What is also confirmed is that the museum remained open, and that visitor services, ticketing, and surveillance continued to operate source.
That is already serious enough. Even without physical security systems being compromised, the disruption to administrative operations — and the potential exposure of sensitive institutional data — is already a significant threat for a heritage institution of this scale.
A cyberattack on a major heritage institution is never a trivial event, even when it does not shut down public access or disrupt the visitor experience.
Museums and historic sites now rely on digital systems not only for administration, but also for coordination, documentation, and day-to-day operational continuity. When those systems are targeted, the impact can spread quickly across the organization source and attackers gain information.
On April 3, 2026, the Uffizi Galleries issued a firm rebuttal to a detailed investigation published that morning by Corriere della Sera. The newspaper had alleged a far more serious breach, claiming that hackers had infiltrated the museum’s network — including systems linked to the Uffizi, Palazzo Pitti, and Boboli Gardens — stolen access codes, internal security maps, camera positions, and even issued a ransom demand directly to the director’s phone.
The museum categorically denied these claims, confirming that a malware attack had indeed targeted its administrative systems on February 1, but stating unequivocally that no data had been stolen or damaged, no passwords or security information had been compromised, and that the attackers had not obtained any maps or operational details.
The Uffizi emphasized that its physical security systems operate on closed internal circuits, independent of the affected administrative network. It described the only tangible impact as the time required to restore backups, while reiterating that visitor services, ticketing, and surveillance had never been disrupted.
The museum also clarified once again that the transfer of items from the Medici Treasury and certain building adjustments were part of pre-planned maintenance and fire-safety compliance work, not emergency responses to the cyber incident.The museum firmly denied those claims, stating that no passwords were stolen, no security map was compromised, and no loss of data had been established source.
For anyone writing about heritage risk, that distinction is essential. A real incident does not automatically validate every alarming claim attached to it.
This is where the debate becomes useful. The Uffizi episode is not best understood as proof that cybercrime had already undermined physical security or fire safety. The evidence does not support that conclusion.
What it does show is something more subtle, and arguably more important: heritage institutions are operating in an environment where digital systems, building management, security procedures, and conservation decisions are increasingly interconnected source.
That interconnection makes communication especially difficult when a crisis unfolds. Measures taken for one reason can be misread as a response to another.
The transfer of the Medici Treasury to a secure vault, for example, was linked by the museum to planned renovation work, not to the cyberattack. Likewise, the closure or sealing of some doors was presented as part of fire-safety and building-compliance measures in a historic structure, not as an emergency action caused by malware source.
In a complex heritage site, several protective processes may be active at the same time, and not all of them belong to the same narrative.
For heritage professionals, this is an important lesson. Cybersecurity matters, but so does precision. Not every digital incident becomes a physical-security breach. Not every operational adjustment is a consequence of the attack. And not every press report should be treated as settled fact before the institution itself has had the chance to clarify what happened source.
Still, the broader warning remains. The Uffizi cyberattack reminds us that museums, archives, and historic sites are no longer insulated from the digital risks that affect every large organization. If their administrative systems are vulnerable, their resilience is vulnerable too.
If communication becomes confused, trust becomes vulnerable as well. And if institutions cannot explain clearly what was affected, what was not, and why certain measures were taken, the public debate can quickly become more dramatic than the incident itself source.
That is why this story matters. Not because it proves that fire safety was compromised, and not because it confirms a catastrophic breach of security information, but because it exposes the need for disciplined, evidence-based risk communication in the heritage sector. In the end, that may be the most valuable lesson of all.
For a broader discussion of integrated risk management in heritage buildings — including the role of access control systems in fire safety — see Cybersecurity in Heritage Buildings: Key Gaps, Vulnerabilities & Practical Mitigation Heritage.